The India IT Act 2000 is the main Indian law governing electronic business and cybercrime. It has been in force since 17 October 2000, with some significant amendments taking effect in 2009 (covering content) and 2011 (covering personal data privacy).
This guide will outline what this act is, who it applies to, how to comply, and what penalties you risk if you don't.
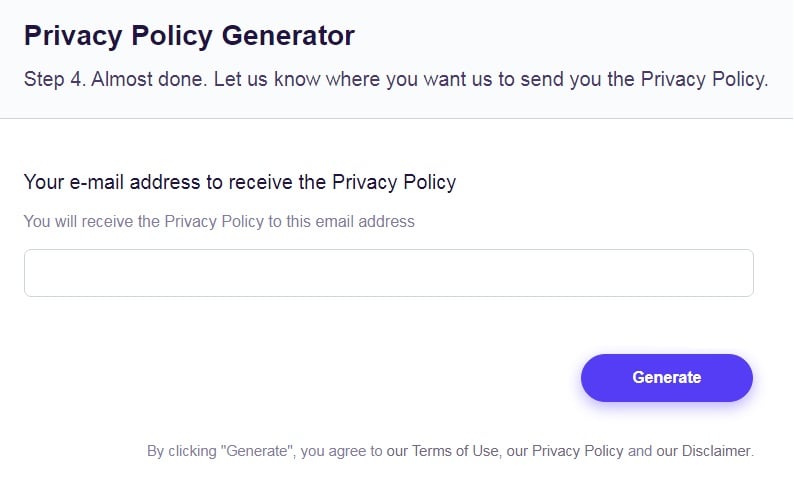
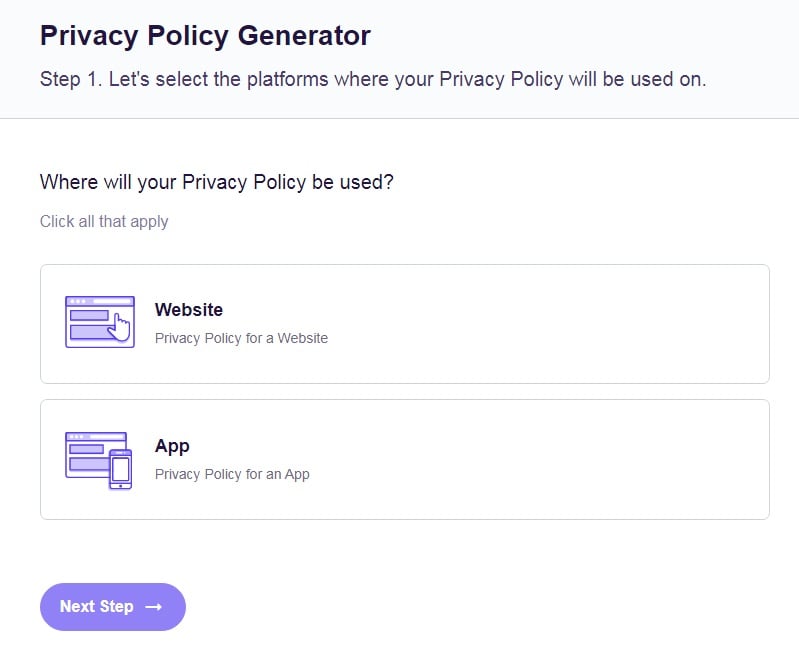
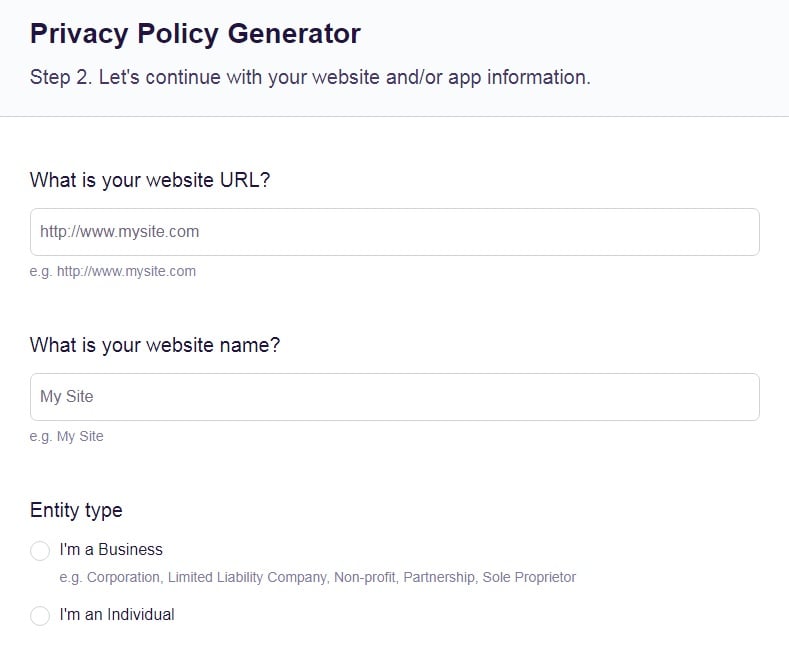
Our Free Privacy Policy Generator helps you create a custom Privacy Policy for your website and mobile app. Just follow these few simple steps and your Privacy Policy will be ready to display in minutes.
- Click on the "Free Privacy Policy Generator" button, located at the top of the website.
- Select where your Privacy Policy will be used:
- Answer a few questions about your business:
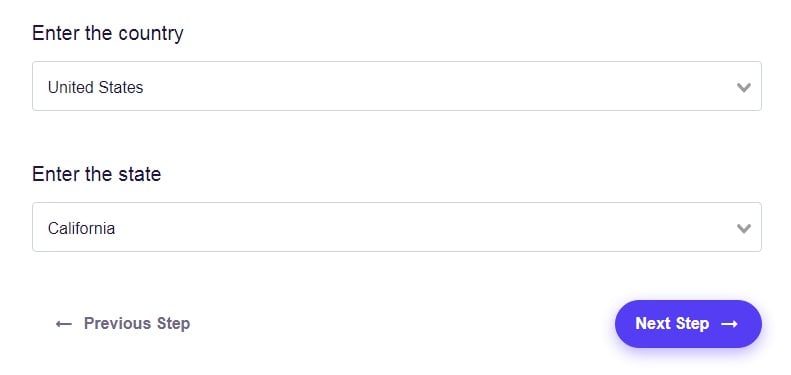
- Enter the country and click on the "Next Step" button:
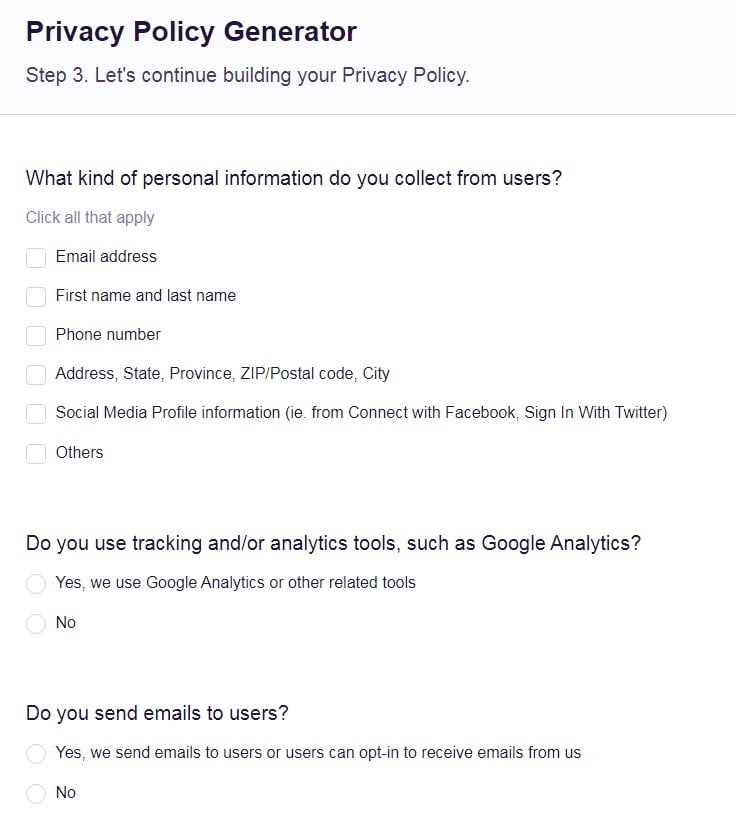
- Continue with building your Privacy Policy while answering on questions from our wizard:
-
Almost done. Now enter your email address where you'd like your new Privacy Policy sent and click on the "Generate" button and you're done.
That's it. Now you can copy and paste your Privacy Policy code into your website, or link to your hosted Privacy Policy.
- 1. Main Components of the India IT Act 2000
- 2. Who Does the India IT Act 2000 Apply to?
- 3. What Does the India IT Act 2000 Require?
- 3.1. Establish a Legal Framework
- 3.2. Avoid Banned Actions
- 3.3. Decrypt Data
- 3.4. Sensitive Personal Data Requirements
- 3.5. Have a Privacy Policy
- 3.6. Have Security Practices in Place
- 4. Complying With the India IT Act 2000
- 4.1. Exemptions
- 5. Summary
Main Components of the India IT Act 2000
The IT act has three main components:
- Creating a legal framework for digital activity and business.
- Banning disruptive actions such as hacking.
- Creating obligations for organizations and businesses
Who Does the India IT Act 2000 Apply to?

The IT act primarily applies to businesses which have a legal or physical presence in India.
This could include:
- Having a registered business in India
- Having offices, factories or stores in India
- Outsourcing to India
- Using servers which are physically in India
The act does not normally apply to a business in another country that simply has users or customers in India. However, it can apply to people outside of India who commit an offence (such as computer hacking) involving a computer or network that is in India. This shouldn't normally affect a legitimately-operating business.
Managers in a business are legally responsible for the actions of the staff they manage. The only exception is if the managers have exercised "due diligence" but remained unaware of the staff's actions.
There are no exemptions for small or medium-sized businesses.
What Does the India IT Act 2000 Require?

The following sections address the requirements and obligations of the IT act.
Establish a Legal Framework
A large part of the act is about establishing a legal framework for doing electronic business in India.
This includes:
- Giving force to electronic signatures
- Treating electronic records in the same way as paper documents
- Appointing officials to oversee the administration of digital signatures
- Exempting internet providers from responsibility for what users do
Avoid Banned Actions
The act also sets out banned actions involving computers and online activities. It's unlikely a legitimate business would break any of these rules but they are worth knowing.
They include:
- Accessing, damaging or disrupting a computer, computer system or computer network without permission
- Using somebody else's password without permission
- Using computer resources for fraud
- Publishing a false digital signature certificate
Businesses to need to pay particular attention to two banned activities:
- Publishing obscene information in electronic form. This is defined as "material which is lascivious or appeals to the prurient interest" so it's important to understand Indian culture before publishing.
- Publishing images of sexual acts.
The act applies to anyone who "publishes or transmits or causes to be published or transmitted in the electronic form." This could be interpreted as covering the operators of a website that allows users to post content. If you fall under the act's scope, you should strongly consider measures such as blocking this feature in India or using moderation before user-generated material appears on your site.
Decrypt Data
India's central and state governments can require data to be intercepted, monitored or decrypted for a broad range of security-related reasons. Unlike with phone tapping, this does not require a public emergency.
When the government uses these powers, you must "extend all facilities and technical assistance" to aid in this interception, monitoring or decryption. Failing to so carries a prison term of up to seven years.
Sensitive Personal Data Requirements
Businesses that collect sensitive personal data must appoint a Grievance Officer. This role is similar to that of a Data Protection Officer (DPO) in other countries and involves handling complaints about processing.
You can only collect sensitive personal data when it is necessary to do so for a lawful purpose of your business.
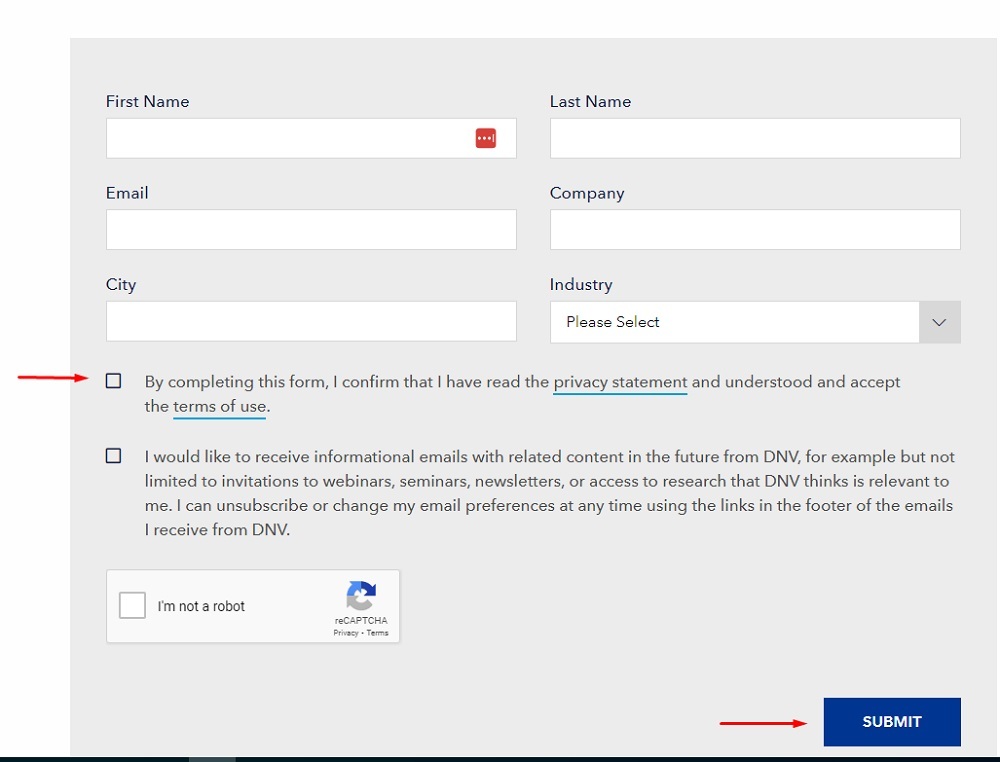
You must have consent to collect sensitive personal data. The government has clarified that this can include electronic communication such as email or completing an online form.
Have a Privacy Policy
You must have a Privacy Policy if you handle any personal data and publish it on your website. The combination of your Privacy Policy and any specific notice you give to data subjects must mean they know:
- That you are collecting data
- The purpose of collecting the data
- Your contact details
- Who will receive the data (who you share it with)
Have Security Practices in Place
You must maintain "reasonable security practices and procedures" to protect any sensitive personal data or information. If you don't, the business is liable for compensation to anyone affected by a data breach.
Complying With the India IT Act 2000

You will need to comply with the act in the following cases:
- You have a business registered or operating in India. (This includes subsidiaries of foreign businesses.)
- You have a physical presence in India such as offices or stores
- You use computer servers located in India
To comply with the law, you need to do the following:
- Be prepared to decrypt data upon a government request.
- Make sure none of your employees do any banned actions such as damaging computer systems or using other people's passwords without permission.
-
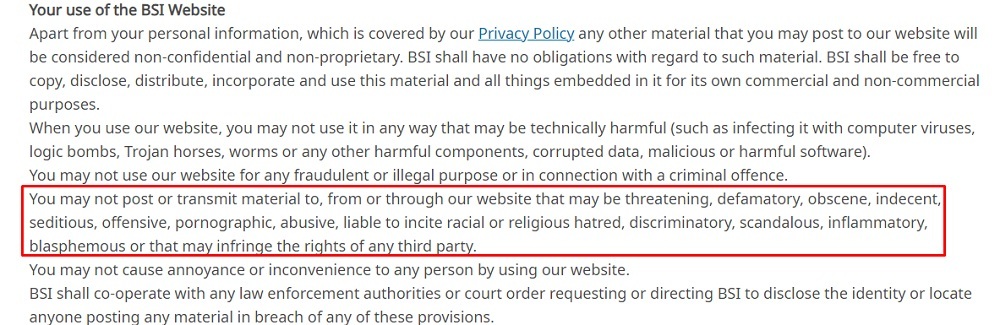
Mitigate the risk that you could be held responsible if your website users post obscene information or images of sexual acts. At a minimum, expressly ban such actions in your Terms and Conditions agreement.
BSI's Terms of Use for users in India expressly bans posting obscene material:
- For maximum protection, either block Indian users from posting content or use advance moderation.
-
Publish a Privacy Policy with your contact details, the information you collect, why you collect it, and who will receive the data.
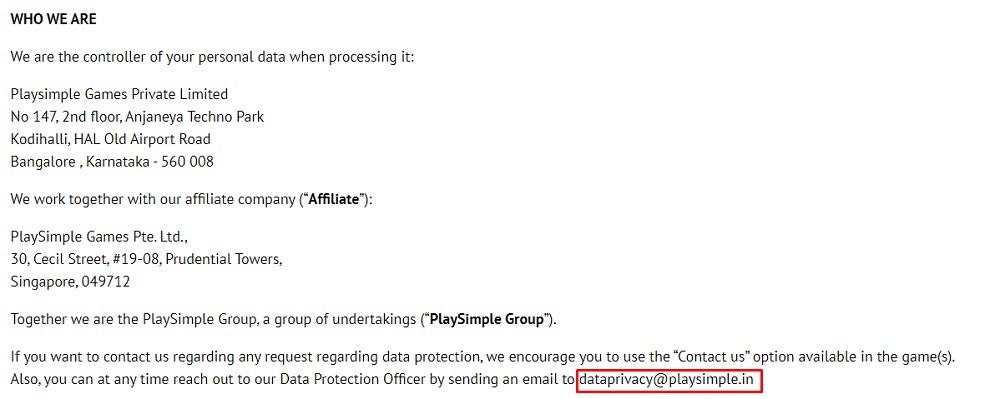
Playsimple gives clear contact details in is Privacy Policy, including an email address and mailing address:
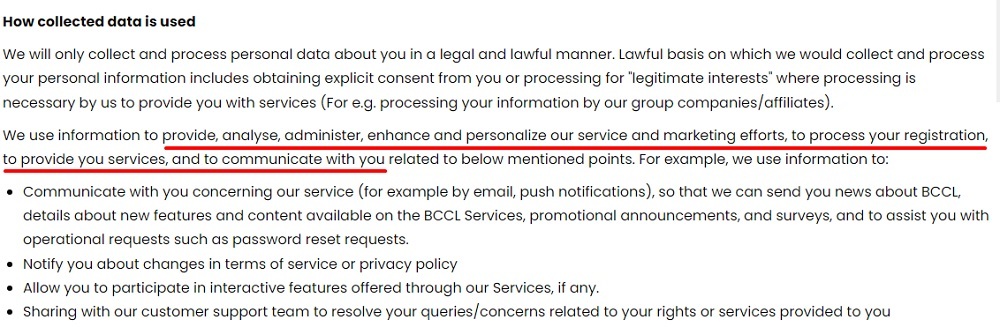
Times Now gives both broad outlines and specific examples of the reasons it collects and uses personal data:
-
Check whether any of your data counts as sensitive personal data. If so you must:
- Appoint a Grievance Officer
- Only collect the sensitive personal data where necessary for a lawful purpose
- Get express consent from users
- Adequately secure the data
DNV requires express consent to data collection and its Privacy Policy by requiring users to tick a checkbox before they can submit a sign-up form:
Exemptions
If you only fall under the scope of the act because you have computer servers in India, the privacy rules don't apply to you.
If you are an outsourcing company, you are exempt from the entire act. In this context, an outsourcing company is one that operates in India but only processes data about people outside of India.
Summary
Let's recap what you need to know about the India IT Act 2000.
The act is the main Indian law on electronic business. Updates to the law added rules on content and data processing and privacy.
It broadly covers businesses that have a legal or physical presence in India, which could include using servers in the country. At the moment, the privacy rules only cover Indian companies.
The act does the following:
- Establishes a legal framework for doing business electronically including recognizing digital signatures
- Bans actions such as hacking, distributing viruses, using passwords without permission, and using computers for fraud
- Bans publication of obscene information or images of sexual acts. (It's possible to interpret this as covering website operators who allow users to post content without moderation.)
- Requires businesses to decrypt data (when possible) upon a government request
The act was updated in 2011 to include privacy rules, though they only cover Indian companies and not those based overseas. The rules largely apply only to sensitive personal information and include:
- Appointing a Grievance Officer
- Having a Privacy Policy
- Getting consent to collect data
- Securing data