If your business is based in, does business in, or has customers in Australia then you are required to follow Australia's Privacy Act of 1988's standards for an individual's right to access their private information.
Australia's Privacy Act provides individuals the right to request access to their personal information along with steps companies and agencies must take when they receive a request. The law does allow some discretion to the companies, but there are some specific steps a business must take to comply with.
Let's take a look.
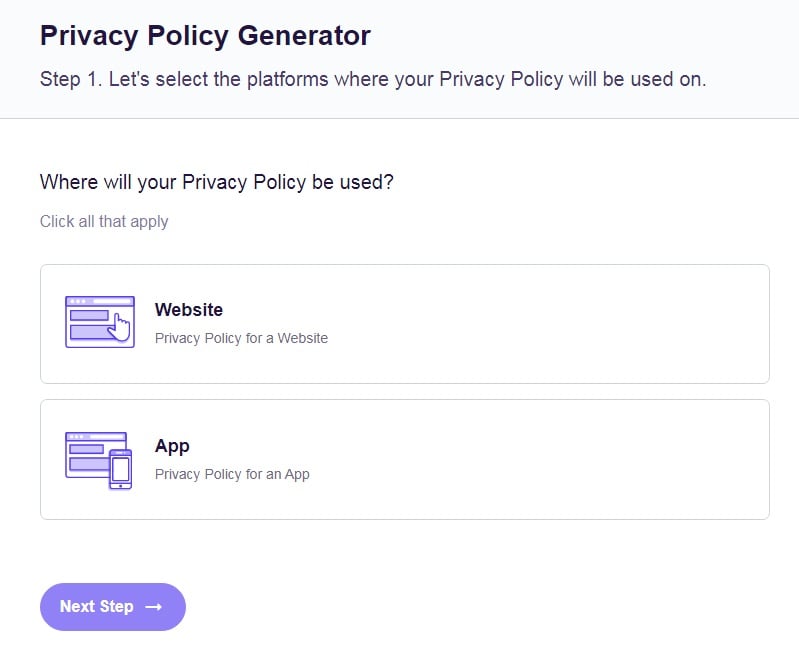
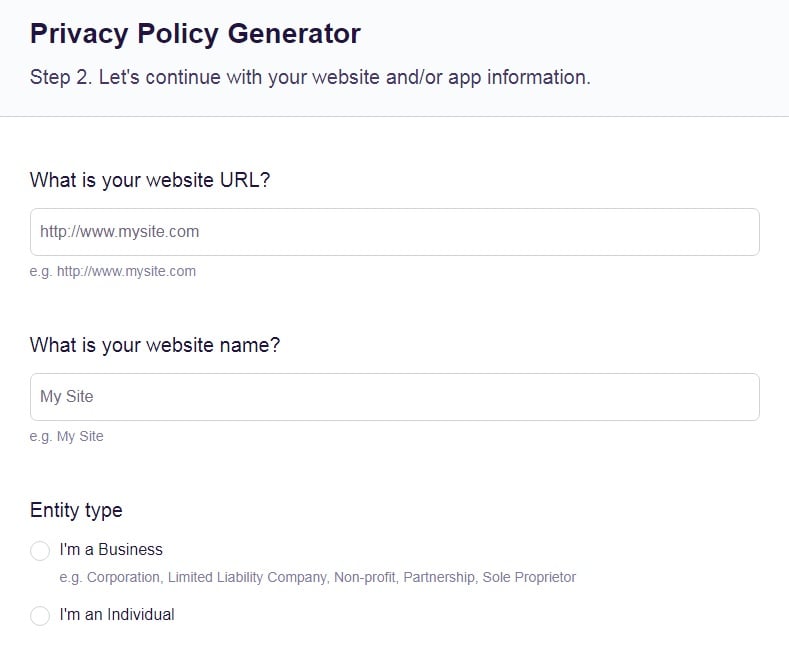
Our Free Privacy Policy Generator helps you create a custom Privacy Policy for your website and mobile app. Just follow these few simple steps and your Privacy Policy will be ready to display in minutes.
- Click on the "Free Privacy Policy Generator" button, located at the top of the website.
- Select where your Privacy Policy will be used:
- Answer a few questions about your business:
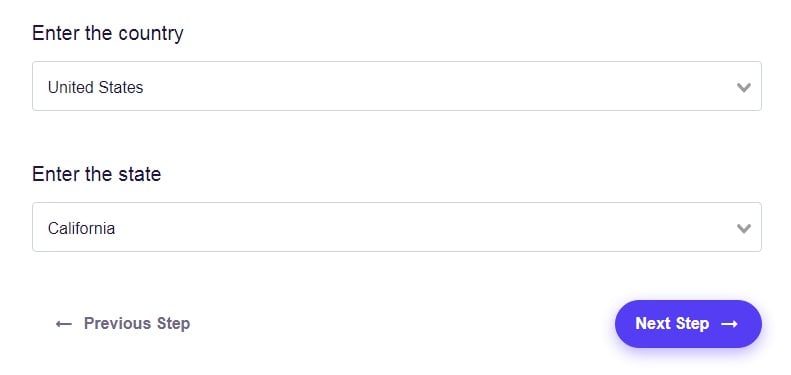
- Enter the country and click on the "Next Step" button:
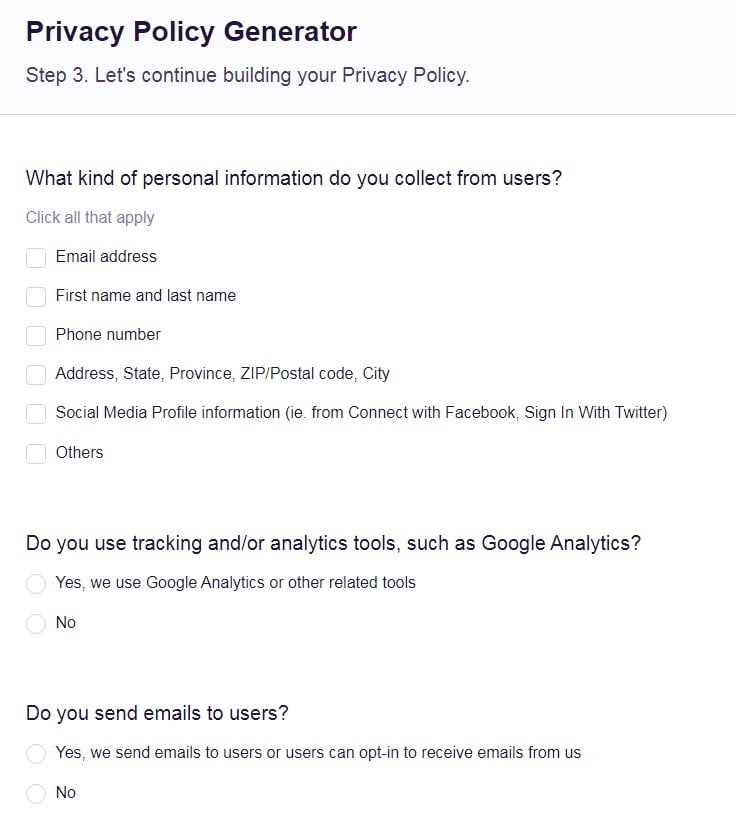
- Continue with building your Privacy Policy while answering on questions from our wizard:
-
Almost done. Now enter your email address where you'd like your new Privacy Policy sent and click on the "Generate" button and you're done.
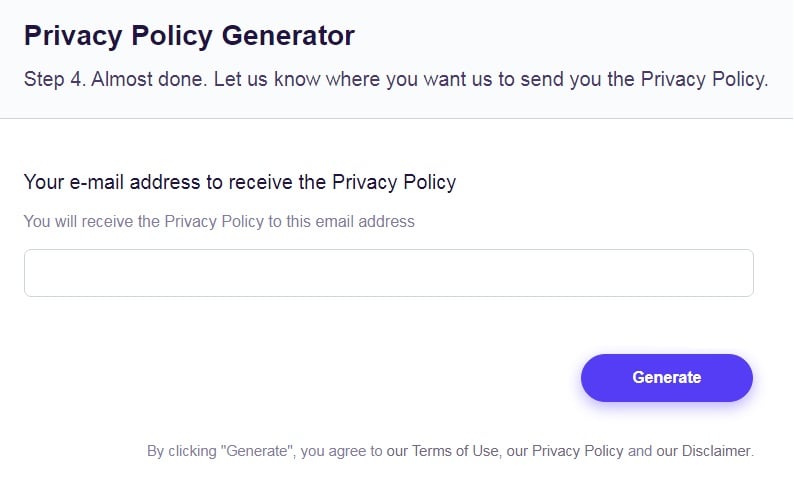
That's it. Now you can copy and paste your Privacy Policy code into your website, or link to your hosted Privacy Policy.
- 1. AU Privacy Act
- 2. The Privacy Access Right
- 3. How is an Access Request Made?
- 4. What to do When You Receive a Privacy Access Request
- 4.1. Step 1: Can you verify the identity of the individual?
- 4.2. Step 2: Can you locate the information?
- 4.3. Step 3: Is there a reason to refuse the request?
- 4.4. Step 4: Charging for Access
- 5. Summary
AU Privacy Act
The AU Privacy Act of 1988 was enacted to protect the sensitive, or private, information of Australian residents and how the information is handled by private companies and federal agencies.
Private information can include name, email address, sexual orientation, religious beliefs, and criminal records.
The Act applies to not only federal Australian agencies but also to the private sector as well. If you are a private entity that has an annual output of over $3 million, then the AU Privacy Act applies to you as well. Both large and small companies would fall under the Act if its turnover is over the $3 million mark.
Entities that would be considered under the act may include:
- Hospitals
- Partnerships
- Gyms or clinics
- Credit reporting agencies
- Childcare centers
- Federal agencies
The act does have some limits to its reach. State or territory agencies, public schools, or political parties aren't under the act's purview. The act was designed to only apply to the private sector and federal agencies. Foreign companies that do business within Australia or have customers in Australia also fall under the act.
The AU Privacy Act's objective was to protect the handling of the personal data of Australian citizens and create a flow of information between the agencies of Australia and foreign countries. The act also regulates credit reporting and health and medical research.
The act's key features businesses should pay attention to are the 13 Australian Privacy Principles (APPs) that are incorporated into the act. The APPs allow entities and agencies to create their own systems to collect and protect sensitive information. However, they still must follow the standards of the APPs and the AU Privacy Act.
The APPs control:
- The use, collection, and transfer of private information
- An entity's obligation with regard to the data
- Rights of individuals to gain access to their sensitive data
- Transparency between the entity and the individual
The Privacy Access Right

A key principle companies should be aware of is the Act gives the right to individuals to request access to their information. Under APP 12, the Privacy Access Right gives an individual the right to request access to their personal information from private entities and federal agencies.
The information can be the person's own information they have provided or their personal information that is connected to another person's (i.e., a marriage certificate).
APP 12 doesn't lay out exactly what a request should look like or how the request should be made. It can be made in writing or informally. The standard leaves the process of how a person may request information up to the business or agency. Even though it has free reign over the process, a company's "access requirements" must still follow the rules of the APP.
APP 12's rules only apply to entities and agencies that "hold" the information. A business is considered to hold the information if "the entity has possession or control of the record that contains the personal information."
The hold definition includes both the physical record and the control of the record. This means if the hard copy is with a third-party and the entity still controls the access to the records, then the entity still holds the record.
How is an Access Request Made?

There is no federally mandated form to request access. Your agency or business can create the process by either an informal or written request. APP 12 suggests that your business makes the requesting process as simple as possible for both your company and the individual.
Australian Unity has a simple, straightforward process for users making access requests. Its process is either calling, emailing or writing to the company with a detailed description of the requested information:
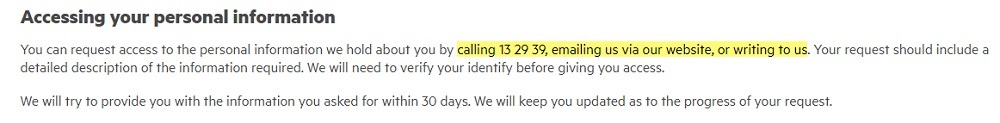
Australian Unity Privacy Policy: Accessing your personal information clause
The request for access must be answered within a "reasonable time" period. Under APP 12, 30 days is the cutoff for most situations.
Businesses or agencies can not charge an individual for requesting access. However, APP 12 does allow you to charge for access if you wish.
What to do When You Receive a Privacy Access Request

Before learning how companies or agencies should process a request, the AU Privacy Act has a couple of requirements when it comes to notifying individuals of their right to request access.
APP 12 does allow entities to create their own "access requirements." The requirements must follow the guidelines including a timeline of the request, how access is to be given, and refusals to the request.
Entities and agencies must notify individuals they have the right to request access to their information through a Privacy Policy. A link to the Privacy Policy should also be easily accessible and clear.
An example of this information can be seen in the Australian Taxation Office's Privacy Policy. The clause notes that the notification an individual has the right to request access to their information and how the ATO responds to the request:
While APP 12 allows entities to create their own requirements, it does lay out a simple general process that should be followed when you receive a request for access.
The process looks like this:
- You receive an access request
- Can you verify the individual's identity? If you cannot, do not disclose personal information. If you can, move on to the next step.
- Can you locate the requested personal information? If you cannot, provide written notice of this to the requesting individual. If you can, move on to the next step.
- Is there any reason to deny access? If not, move on to the next step.
- Can access be provided in the manner requested? If not, can it be provided by any other means?
- Decide if you will charge for access.
- Provide access.
Let's look at each step more in detail.
Step 1: Can you verify the identity of the individual?
If a business receives a request for access the first step is to verify the identity of the individual. A request for access can be made by:
- The actual individual
- Legal guardian
- Authorized agent
- Power of attorney
Companies can identify the individual by personal documentation such as a passport or other legal items of identification. If the information is more sensitive than most, determining the identity may require other processes.
The AU Privacy Act prefers businesses and agencies to sight the documents and not copy them. This can be done by either meeting with the individual in person or over the phone by correlating with other records. This regulation acts as a further way to protect the private information of the individual.
If the individual can not be identified, then the company or agency must not disclose information. If you can, go to Step 2.
Step 2: Can you locate the information?
The information requested must be under a business or agency's "hold." A business must have possession or control of the documents. The documents can include emails, hard copies, and even electronic calendars. The request must be to specific documents. A business does not have to provide information that is outside the scope of the request.
Reasonable measures must be taken by companies to locate the information. These reasonable measures include:
- Checking with staff and contractors
- Searching own databases
- Contacting outsourced third-parties
If the information cannot be located, then a business must provide written notice of this to the individual. If the information is located, go to Step 3.
Step 3: Is there a reason to refuse the request?
A business may refuse access to information for ten specific valid reasons laid out in APP 12.
The reasons are:
- Access would pose a serious threat or health of an individual or to public safety
- Unreasonable impact on the privacy of other individuals
- Frivolous or frustrating request
- Information is part of legal issues between the company and the individual
- Disclosure would prejudice negotiations
- Disclosure would be unlawful
- Required by law
- Suspect unlawful activity
- Disclosure would hinder a law enforcement investigation
- Information related to commercially sensitive decision-making
Businesses or entities should include the right to refuse a request for access in their Privacy Policies. A company or entity can either clearly state the reasons for refusing, or provide a general statement.
Here's how Bond University reiterates APP 12's reasons instead of a general provision:
If a valid reason is identified, APP 12 requires companies to see if there are other means to provide the information. A business can either give a summary of the information, redact sensitive information, allowing the individual to review the hard copies and take notes, or using an intermediary.
If there is no other way to provide the information and the request is refused, you must provide written notice to the individual.
The notice must include the reasons why the request was refused, how the individual may file a complaint, and how the complaint process works. The notice should also provide options an individual may take to file outside complaints such as dispute schemes or with the Office of Australian Information Commissioner (OAIC).
If there is no reason to refuse and access is granted, go to Step 4.
Step 4: Charging for Access
APP 12 does allow businesses or agencies to charge individuals for access to their records, but not for requesting access their records. The charge must not be excessive and should not be used as a way to deter individuals from making a request. Excessive charges depend on the company but can include getting legal advice or using a higher rate for staff work.
The charges can include:
- Staff costs for searching for records
- Staff costs for producing and sending information
- Postage
- Use of intermediary (when applicable)
Agencies or businesses may also state in their Privacy Policies whether they charge for access and the factors that are considered in the price.
Here's how Australian Government Solicitor does this in its Privacy Policy:
Businesses should provide options for individuals to choose that may help reduce the cost of access. This can be either switching from mailing hard copies to sending electronic copies.
Once a charge has been agreed upon then a business may provide the information to the individual.
Summary
The AU Privacy Act of 1988 gives the right to individuals to request access to their information from private companies or federal agencies in Australia. The law was created to protect private information and create a transparent relationship between an individual and a business.
Businesses that receive a request for access can follow these simple steps to comply with the law:
- Step 1: Can you identify the individual?
- Step 2: If you can identify, can you locate the information?
- Must "hold" the information.
- Step 3: If you locate the information, is the disclosure refused for a valid reason?
- If refused, you must provide written notice.
- Are there other means to provide the information?
- Step 4: Charges for Access
- If information can be provided, you may charge for the access, but not for making the request.