The New York SHIELD Act may well cover your business even if you aren't located in the state of New York. The act significantly increases the burden on businesses to not only protect customer data, but to act quickly to limit the risk and damage from any occurring data breach.
Here's what you need to know about the act, and what you'll need to do to avoid facing penalties for non-compliance.
Use FreePrivacyPolicy.com to generate the necessary legal agreements for your website/app:
- Free Privacy Policy Generator
- Free Terms and Conditions Generator
- Free Cookies Policy Generator
- Free Disclaimer Generator
- Free EULA Generator
- Free Return & Refund Policy Generator
You check our Free Cookie Consent to start making your business legally compliant with the Cookies Directive in the EU.
- 1. Background and Key Points of the SHIELD Act
- 2. The SHIELD Act's Expanded Scope
- 2.1. Location
- 2.2. Data
- 2.3. People
- 3. Security Requirements Under the SHIELD Act
- 3.1. Exemptions to the Security Requirements
- 4. Notification Requirements Under the SHIELD Act
- 4.1. Recipients
- 4.2. Content
- 4.3. Exemptions
- 5. Penalties and Remedies for SHIELD Act Non-Compliance
- 6. Summary
Background and Key Points of the SHIELD Act
The SHIELD Act is formally titled the Stop Hacks and Improve Electronic Data Security Act. It's a state law that took effect in two stages with some measures effective from October 23, 2019 and the rest effective from March 21, 2020. It expanded the scope of existing state rules on breach notifications in several ways as well as adding new rules on data security.
At its simplest, the SHIELD Act requires data controllers to do two things:
- Properly secure personal data through a range of measures
- Report any data breach to the people affected and to state officials
Unlike some similar laws, the SHIELD Act doesn't create any personal data rights for individuals or give them ways to enforce or exercise such rights.
The SHIELD Act's Expanded Scope

Location
Previously, New York's data laws only covered businesses that operated in New York. SHIELD expands that scope and it now covers any individual or business that "owns or licenses computerized data which includes private information" about a resident of New York state.
The new rules apply regardless of where the data controller is based, operates or has a physical presence. Instead it's solely about where the data subject lives.
Data
The SHIELD Act expands and clarifies what data comes under the requirements. The rules about breach notifications apply when "private information" is accessed without authorization.
In most cases "private information" means a combination of:
- A piece of personal information, meaning anything that identifies an individual, and
- A specific type of information known as a "data element"
The following combinations count as "private information" unless the data element is encrypted and the encryption key remains secret:
- Personal information plus a social security number, a driver's license number or a non-driver identification number
- Personal information plus a financial account or card number and any necessary credentials (such as passwords or codes) to access a financial account
- Personal information plus biometric information used to identify or authenticate somebody
"Private information" also covers the combination of a user name/email address and a password/security question answer allowing access to an online account. This combination counts as private information even if it doesn't include any personal information.
People
The SHIELD Act covers private information about any individual who resides in New York state. This contrasts with similar laws elsewhere which only covers consumers. Note that this means the SHIELD Act does cover information a business stores about employees.
Security Requirements Under the SHIELD Act

Anyone who owns or licenses private information about a New York resident must have a data security program. The SHIELD Act specifies that this program must include the following:
- Reasonable administrative safeguards
- Reasonable technical safeguards
- Reasonable physical safeguards
The law doesn't set out specific requirements beyond these three points. However, it does list 14 examples of safeguards:
- Name an employee or employees to coordinate data security.
- Identify internal and external risks.
- Check you have sufficient safeguards against these risks.
- Train staff on security procedures.
- Use service providers who also have adequate safeguards and make this a contractual requirement.
- Change and update your security program when necessary.
- Assess risks in your networks and software.
- Assess risks in your data processing, transmission and storage.
- Have measures to detect, prevent and respond to cyber-attacks.
- Regularly test your security measures.
- Assess risks in your physical data handling.
- Have measures to detect, prevent and respond to physical intrusions.
- Protect against unauthorized access to the private information at any time.
- Irretrievably delete private in a reasonable time after you no longer need it.
Remember that these are simply examples rather than an exhaustive list of measures. You should use any other measures that help ensure a reasonable degree of safeguarding against unauthorized access.
Though the SHIELD Act doesn't require you to do so, you can build trust with customers by detailing your security safeguards in your Privacy Policy as in this example from HERE Global:
Belmond notes that it has followed one of the SHIELD Act's specific example safeguards:
Exemptions to the Security Requirements
The SHIELD Act allows for two exemptions to the security requirements. The first is that you are automatically treated as compliant if you already comply with the security requirements of any of the following other laws:
- The Gramm-Leach-Bliley Act
- HIPAA regulations
- Title 24, Part 500 of the New York Code
- Any other relevant rules from the Federal or New York state governments and their associated bodies
There's also an exemption for businesses that meet at least one of the following three criteria:
- Have fewer than 50 employees
- Have a gross annual revenue of less than $3 million in each of the past three fiscal years
- Have year-end total assets of less than $5 million
Notification Requirements Under the SHIELD Act

The SHIELD Act's notification requirements are triggered whenever a data breach takes place. This is defined as any unauthorized access to private information about a New York state resident. That's a big change to the previous law in New York, which only covered unauthorized "acquisition."
The SHIELD Act's definition of unauthorized access is broad and covers somebody viewing, communicating with, using or altering the data without authorization. It also covers cases where you don't know for certain somebody accessed the data but reasonably believe that's the case.
Recipients
Following a data breach triggering the notification requirement you must send a notification to the following people:
- Anyone affected by the breach (that is, the people the private information is about)
- The owner of the relevant data if you license it rather than own it yourself
You must also give the following people and organizations details about the notification, including when it's going out, what it says, and how many people will get it:
- The state Attorney General
- The New York Department of State
- The state Office of Information Technology Services
You must also send these details to consumer reporting agencies if you will be notifying more than 5,000 New York residents.
Content
The notification must include the following information:
- Your contact details
- Phone numbers and websites for state and federal agencies and other bodies that can give information about how to deal with personal data breaches and prevent identity theft
- The types of information that were accessed without authorization (For example, your credit card number or your email address and password)
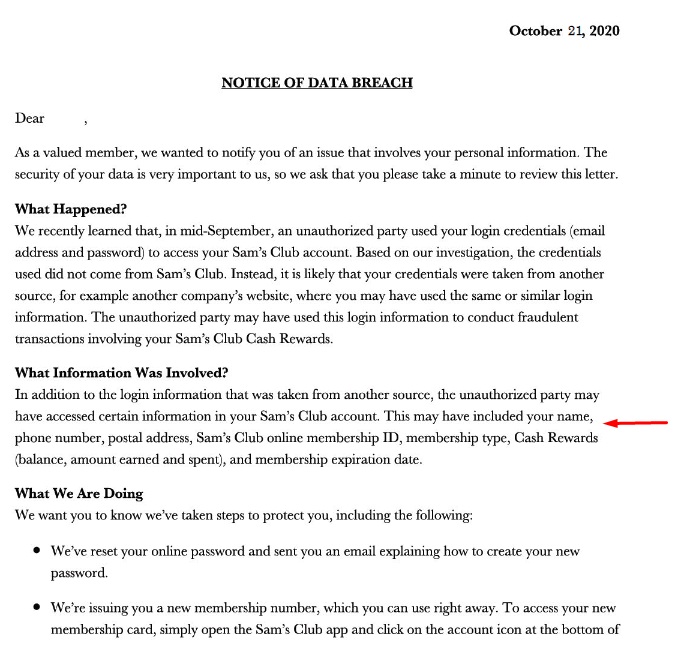
This example from Sam's Club would comply with the requirement to detail the type of information accessed:
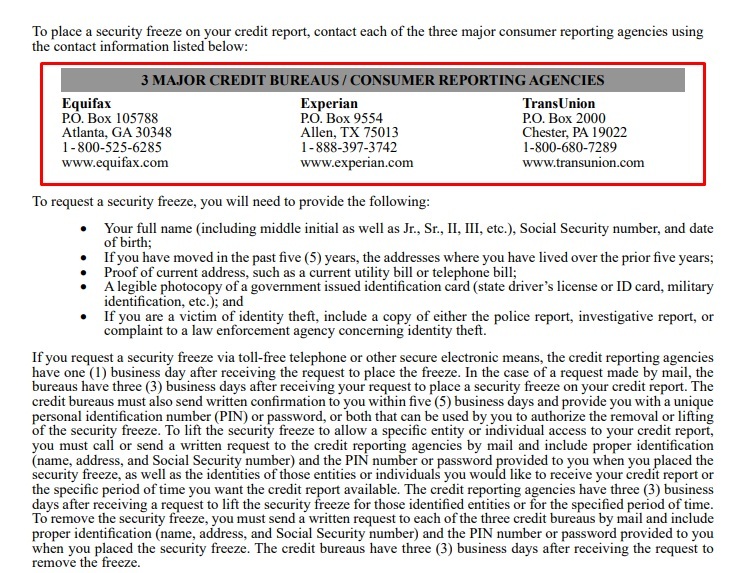
This example from Wyndham Capital would comply with the requirement regarding bodies that can help deal with the consequences of a data breach:
Exemptions
The SHIELD Act offers two key exemptions from the notification requirements.
The first is in the case of an "inadvertent disclosure by persons authorized to access private information."
An example might be an employee mistakenly opening the wrong files or emailing them to the wrong colleague.
This only applies if you assess the situation and reasonably decide the exposure of the data won't lead to it being misused or causing the data subjects emotional or financial harm.
You must make and keep a note of this decision for at least five years. If the exposure involves data about more than 500 New York state residents, you must send a copy of the decision to the state attorney general within 10 days of making it.
The second exception is if you've already notified the affected data subjects about the breach under another law (federal or state).
This could include the Gramm-Leach-Bliley Act for financial data or HIPAA for health data. When this happens you must still tell the state Attorney General, New York Department of State, Office of Information Technology about the breach as you normally would.
Unlike with the security procedure requirements, there's no small business exemption from the notification requirements.
Penalties and Remedies for SHIELD Act Non-Compliance
Breaches of the SHIELD Act can lead to civil action by the state attorney general. Individuals can't bring a case themselves under the act.
If you breach the security requirements, a court can impose a civil penalty of up to $5,000 per breach.
If you "knowingly or recklessly" breach the notification requirements, a court can impose a penalty of up to $20 for each person you failed to notify, subject to a minimum total of $5,000 and a maximum of $250,000. It can also order you to pay the actual damages and costs of the people affected by your failure to notify them.
If you breach the notification requirements but don't do so recklessly or knowingly, the court cannot impose a penalty. It can order you to pay the actual damages and costs of the people affected by your failure to notify them.
Summary
Let's recap what you need to know about the New York SHIELD Act:
- The act applies to any individual or business that owns or licenses private information about a New York state resident. It doesn't matter where you are based, just the person the information is about.
- Private information is usually a combination of personal information (something that identifies an individual) and one of several named "data elements" such as card numbers, identity numbers and biometrics. The main exception is data stored in encrypted form where the encryption key is kept secret.
- A combination of details that allows access to an online account also counts as "private information" even if it doesn't identify an individual.
- You must safeguard private information through reasonable safeguards. These must include administrative, technical and physical safeguards.
- You must notify affected people after a data breach. The main exception is an accidental breach involving an authorized person. This exception only applies if you believe it won't cause any harm or lead to misuse.
- The notification must list your contact details, those of organizations that can help prevent or deal with identity theft, and information about the type of data that was accessed.
- You must tell the state Attorney General, New York Department of State and Office of Information Technology when you are making a notification.
- Penalties for breaking the law include $5,000 for breaching the security requirements and between $5,000 and $250,000 (depending on the number of people affected) for knowingly or recklessly breaching the notification requirements. You may also have to pay actual damages for losses resulting from your failing to make the notifications, even if your failure wasn't knowing or reckless.